Sanya Morang (sanya@seductionoffraud.com) is Vice-President of Research & Development for the San Francisco Chapter of the Association of Certified Fraud Examiners, and Steve Morang (steve.morang@yahoo.com) is President of the same chapter.
For decades, the anti-fraud profession has relied on the Fraud Triangle[1] to explain white collar crimes such as embezzlement. With its key attributes of pressure, opportunity and rationalization, the fraud triangle, attributed to Dr. Donald Cressey, was first introduced in the 1950s. He used it to explain the mind-set of persons committing embezzlement and similar breaches of trust. Since then, many professional organizations, such as the Association of Certified Fraud Examiners (ACFE), the American Institute of Certified Public Accountants (AICPA), and the Institute of Internal Auditors (IIA), have embedded the Fraud Triangle into their professional education as a cornerstone to understanding fraud.
However, many of the largest scandals we have seen in recent years (e.g., Wells Fargo, Volkswagen, Toshiba, Theranos) no longer fit nicely into the Fraud Triangle. Moreover, many of these scandals share a number of the same characteristics. These are not traditional “trusted bookkeeper” embezzlements of yesteryear, but global scandals carried out by some of the world’s most renowned and respected companies and business leaders. What is going on? Why are we as anti-fraud, ethics, and compliance professionals being caught off guard by these events? The answer is because we are framing these scandals and frauds using an outdated lens. We have relied on tools from the past to explain current events that no longer fit into the previous models. We need to fundamentally change the way we look at human behavior and ethics if we want to become better at fraud prevention, detection, and investigation. How do we do this? By using a new tool developed to address many of today’s issues: the Seduction of Fraud Diamond (SoF Diamond, see Figure 1).
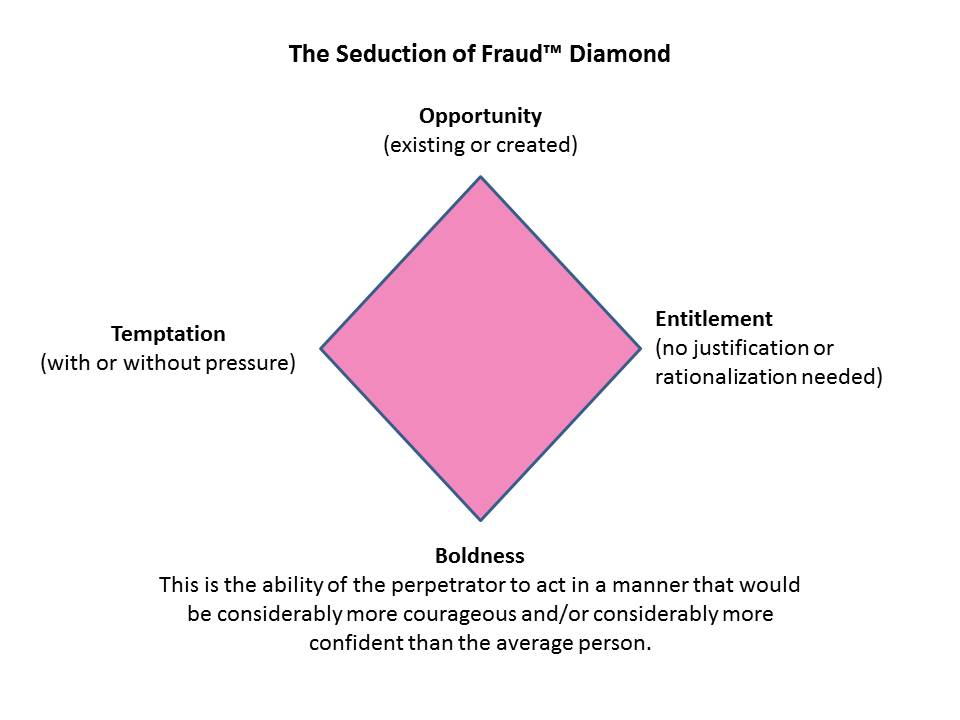
The SoF Diamond enhances the previous attributes of the Fraud Triangle and adds a fourth dimension to it. The new attributes are temptation, entitlement, opportunity, and boldness. Let’s take a closer look at each of these to understand how they compare to Cressey’s Fraud Triangle.
Temptation
This speaks to the motive behind why someone commits the fraud in the first place. In Cressey’s model, the good person had to have at least a “perceived” financial pressure to steal. In other words, if they had no perceived need, they would not steal. However, we are seeing more and more often persons who are clearly not under the traditional financial pressure committing fraud. From successful CEOs to young Silicon Valley billionaires, they are simply turning to fraud and other unethical behaviors. They have a need that is not financial, but internally driven by narcissistic tendencies. In other words, they are seduced to committing fraud by power and control. A great recent example of this is the rise and fall of the founder and former CEO of Uber, Travis Kalanick, who was removed from the company for multiple unethical acts.[2]
Entitlement
In Cressey’s triangle, the good person would need to rationalize their behaviors to justify their bad or evil actions. This attribute, by definition, only addresses those persons with a functioning moral compass that convicts them of their actions: “Stealing is bad, so I will just borrow some money and pay it back later.” However, for someone whose personality is dominated by a sense of entitlement, there is no underlying need to rationalize their behaviors. Entitlement is not a rationalization. Entitlement completely removes the need to rationalize one’s actions. Therefore, “As long as I want to do it, I will,” regardless of how a “normal” person would classify this behavior on the moral compass. For example, take Elizabeth Holmes of Theranos who put her personal goals above that of the well-being and health of patients.[3]
Opportunity
Without the opportunity to commit fraud, nothing can really happen. That is why many fraud prevention activities conducted by professionals, such as accounting and auditing professionals, focus on addressing opportunity and shutting this attribute down as much as possible. However, as we will see in the next attribute, this can only have limited success if not addressed holistically with the other attributes of the SoF Diamond.
Boldness
This is the attribute that brings the SoF Diamond all together. It drives the ability to follow temptation, embrace entitlement, and circumvent even the most well-designed internal controls. For the purposes of the SoF Diamond, boldness is the ability of the perpetrator to act in a manner that is considerably more courageous and confident than that of the average person. In many situations, being bold can be helpful. However, it is boldness without a sense of integrity that can lead to disaster. Many recent frauds have happened in organizations with a strong internal control environment; however, through boldness, fraudsters are able to circumvent even the most stringent of controls, in ways and manners that most professionals would consider all but impossible. Take for example the fraud of Mr. Oh, the treasurer and ethics ombudsman of ABB Korea. Over the course of just 18 months, he was able to embezzle more than $100 million. To do this, he had to repeatedly lie, falsify documents, and remove company stamps from his office, all while listening to complaints, giving ethics training, and coordinating the internal and external audits of the subsidiary. Although there were weaknesses in the internal control environment, it was only through his ability to be bold in the face of it all that allowed him to pull it off and disappear without a trace.[4]
Conclusion
As compliance and ethics professionals, you need to take a step back and understand you will often be facing individuals who do not necessarily fit into the “normal” and “good” framework. Because of this, you should consider updating your toolbox with the SoF Diamond model to help your analysis in today’s fast-moving, ever-changing environment. Furthermore, by learning more about the similarities in personality traits of historical seducers such as Cleopatra and Casanova and modern-day fraudsters such as Elizabeth Holmes and Bernie Madoff, you can continue to develop your understanding of human behavior and bridge the gap between ethical conduct and fraud prevention.
Takeaways
-
Tools and techniques used in understanding fraudsters need an update.
-
Narcissistic personalities are becoming more prevalent today, which leads to a new dimension when trying to understand the motivations behind actions.
-
Boldness is a key personality trait that needs to be assessed when conducting investigations or fraud risk assessments.
-
When dealing with a breach of ethics, you cannot assume that the person you are dealing with is a normal “good” person with a functioning moral compass.
-
The ultimate goal of seduction is to gain power and control.